Morbi et tellus imperdiet, aliquam nulla sed, dapibus erat. Aenean dapibus sem non purus venenatis vulputate. Donec accumsan eleifend blandit.
Cloud Security Challenges in the Modern World
Cloud security has become a critical concern for businesses and individuals who store data in the cloud. As organizations increasingly migrate to the cloud, the importance of protecting sensitive information from breaches, attacks, and data loss grows exponentially. Cybercriminals exploit vulnerabilities in cloud systems to access valuable data, underscoring the need for companies to understand […]
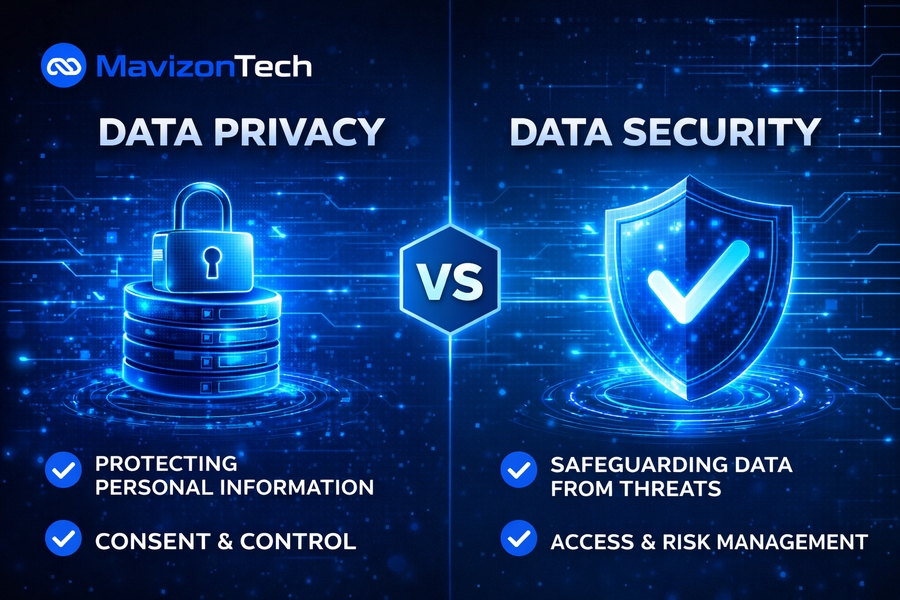
Read MoreData Privacy vs Data Security: Key Differences Explained
The importance of data in our digital age cannot be overstated. With the rise of online platforms, the collection and storage of personal information has become central to businesses, governments, and other entities. This has led to the development of concepts like data privacy and data security, which are critical for protecting sensitive information. Although […]
Read MoreWhy is Data Security Important?
Data security has become an essential element for businesses and individuals alike in today’s digital world. As cyber threats continue to evolve, safeguarding sensitive information from unauthorized access, corruption, or theft is of utmost importance. This article explores the significance of data security, the potential risks of data breaches, and the strategies you can implement […]
Read MoreCyber Security vs Network Security : Key Differences Explained
In today’s increasingly connected world, understanding the difference between cybersecurity and network security is crucial. Both are essential in safeguarding data, networks, and systems from cyber threats, but they focus on different aspects of protection. Cybersecurity is a broad discipline that covers all aspects of digital security, while network security is a subset of cybersecurity […]
Read MoreMozRank Checker by Alaikas: SEO Link Score Help
If you’ve ever wondered why two pages with similar content rank differently, the answer often lives in the link profile. Search engines still treat links as signals of trust, relevance, and authority—especially when those links come from strong pages. That’s where mozrank checker by alaikas becomes useful. Instead of relying on vague “my SEO is […]
Read MoreWill AI Replace Cybersecurity? An In-Depth Look for the U.S. Audience
In an era where digital threats grow by the hour and cyber-defenses must constantly evolve, you might ask: will AI replace cybersecurity? The reality is nuanced. Yes, artificial intelligence is transforming how cybersecurity works, but no, it won’t simply replace the human defender. In this article you’ll learn the current role of AI in cyber-defense, […]
Read MoreCyber Security Risk Assessment Made Simple & Effective
In today’s digital world, you face an ever-evolving threat landscape where malicious actors seek to exploit weaknesses in your organisation’s systems. A cyber security risk assessment gives you a structured way to identify your most critical assets, understand the threats and vulnerabilities they face, prioritise the risks, and decide how to reduce them in line […]
Read MoreBusiness Security Tips You Can’t Ignore
When you’re running a business, every asset—from your data to your physical premises—needs safeguarding. If you leave vulnerabilities open, you don’t just risk theft or damage; you risk your reputation, your customer trust, and your bottom line. With threats evolving fast, you must stay one step ahead. In this article you will learn actionable strategies […]
Read MoreBenefits of Cyber Security in Business: Why It Matters Today
You operate in a digital world where attackers target businesses of every size with ever-evolving threats. If you embrace robust cyber security, you won’t just avoid disasters—you’ll gain resilience, trust and strategic advantage. In this article you will learn how biometric protection supports operations, why business continuity depends on strong defense, what cost and reputation […]
Read MoreWhat Is ACL in Cyber Security: Access Control Explained Clearly
In the rapidly evolving world of cyber security, maintaining robust network defenses is essential. One of the foundational tools used in controlling traffic and restricting unauthorized access is the Access Control List (ACL). But what is ACL in cyber security, and why is it so critical in today’s digital defense strategies? At its core, an […]
Read More