Morbi et tellus imperdiet, aliquam nulla sed, dapibus erat. Aenean dapibus sem non purus venenatis vulputate. Donec accumsan eleifend blandit.
Klaviyo Marketing Agency Funnel Flux: Early Awareness To Urgency Deal Dominance
The funnel is no longer a ladder. It is current. Funnels used to be steps. Now they are flowing. Buyers don’t descend anymore. They drift, loop, pause, compare, disappear, return, and sometimes surge straight to a decision in a single session. The linear funnel is collapsing under real behavior. Multi-session journeys have replaced neat stage […]
Read MoreHow IP Geolocation Strengthens Your Cybersecurity Defense Strategy
The era of a quantum leap in modern technologies such as artificial intelligence, combined with rapid digitalization, has allowed business owners to go online. Since that, online safety has become increasingly vital. The Global Security Outlook 2026 reported that last year more than 70% of organizations fell victims to fraud. Are there tools that can […]
Read MoreHow Video Platforms Deliver Content at Scale
YouTube ingests 500 hours of video every minute. Netflix handles 260 million subscribers across 190 countries. A decade ago, numbers like that would have crashed everything. Now nobody even thinks about it. That invisibility is intentional. When you hit play on a video, the whole point is that nothing seems to happen. You just watch. […]
Read MoreUnderstanding Traffic Origin in Modern Web Systems
Every website processes thousands of connection requests daily, and each one carries identifying information about its source. The IP address attached to incoming traffic tells servers where requests originate, what network they travel through, and whether they deserve trust or suspicion. For businesses running web operations at scale, understanding traffic origin isn’t optional. It’s the […]
Read MoreCloud Security Challenges in the Modern World
Cloud security has become a critical concern for businesses and individuals who store data in the cloud. As organizations increasingly migrate to the cloud, the importance of protecting sensitive information from breaches, attacks, and data loss grows exponentially. Cybercriminals exploit vulnerabilities in cloud systems to access valuable data, underscoring the need for companies to understand […]
Read MoreThe Technology Behind Modern Event Command Centers
There’s a lot that goes into keeping crowds safe during sporting events. From perimeter security to threat assessments and coordinated response efforts, mass gatherings require a ton of behind the scenes activity to maintain safety and security. But did you know… Each of these moving pieces need to connect back to a single central hub. […]
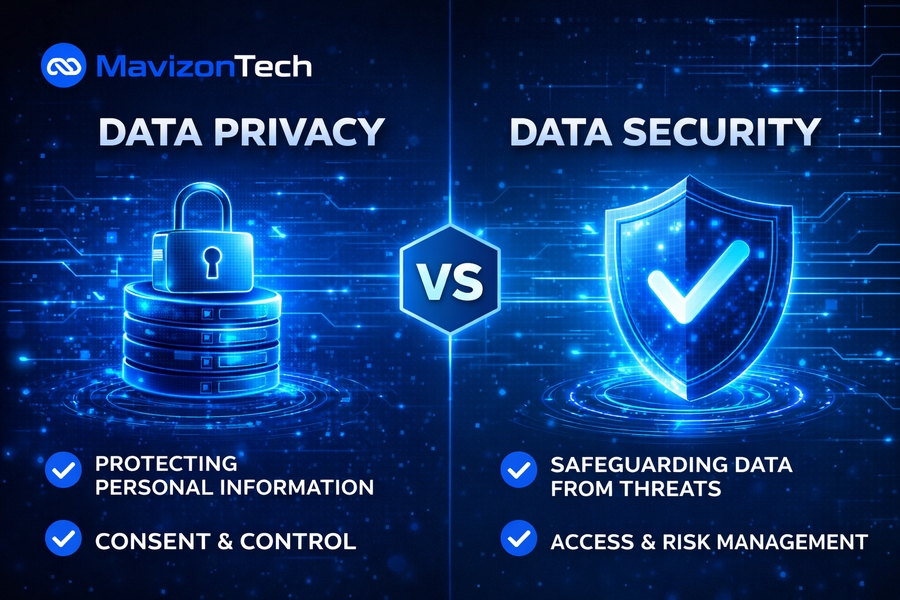
Read MoreData Privacy vs Data Security: Key Differences Explained
The importance of data in our digital age cannot be overstated. With the rise of online platforms, the collection and storage of personal information has become central to businesses, governments, and other entities. This has led to the development of concepts like data privacy and data security, which are critical for protecting sensitive information. Although […]
Read MoreWhy is Data Security Important?
Data security has become an essential element for businesses and individuals alike in today’s digital world. As cyber threats continue to evolve, safeguarding sensitive information from unauthorized access, corruption, or theft is of utmost importance. This article explores the significance of data security, the potential risks of data breaches, and the strategies you can implement […]
Read MoreCyber Security vs Network Security : Key Differences Explained
In today’s increasingly connected world, understanding the difference between cybersecurity and network security is crucial. Both are essential in safeguarding data, networks, and systems from cyber threats, but they focus on different aspects of protection. Cybersecurity is a broad discipline that covers all aspects of digital security, while network security is a subset of cybersecurity […]
Read MoreBenefits Of Network Security For Modern Businesses
Network security is no longer optional in today’s digital world, where cyber threats evolve every day. Whether you run a small business or manage a large enterprise, protecting your network ensures your data, systems, and reputation remain intact. Without proper safeguards, even a minor breach can result in financial losses and operational downtime. In this […]
Read More